Did you know that, from your bedroom, with less than $100 of equipment, you too can learn about confidential corporate mergers, secret government relations, and cockpit inside jokes?
Chatty aircraft
Every good secret needs good informants. In our case, it turns out that planes are surprisingly talkative and constantly emit a wide range of radio signals while in flight. This article focuses on two such systems:
ADS-B/C
Automatic Dependent Surveillance–Broadcast, initially designed among other goals to avoid collisions, continuously broadcasts telemetry data such as the position, speed, altitude, etc. of a given aircraft. It is generally mandatory for public aviation whereas business, state or military aircraft may sometimes operate under exemptions.
A decoded ADS-B signal typically looks like this:
UPS267 | hex a48850 | lat 46.679901 | lon 9.534391 | alt 38000 ft | gs 421.3 kt | track 346.13° | squawk 2744From left to right, we have:
- Flight ID
- ICAO, 24-bit identifier assigned to each aircraft
- Position
- Altitude
- Ground speed
- Direction (346.13° is almost due north, slightly west of north)
- Transponder squawk code
ADS-C, Automatic Dependent Surveillance–Contract, is ADS-B's sister. Unlike ADS-B, however, which is broadcast openly, ADS-C sends structured surveillance reports to specific ground systems under a reporting “contract”. It is mostly used in remote and oceanic areas, often over satellite links, and communicates not only an aircraft’s position, but sometimes also route and intent information.
ACARS
The Aircraft Communications, Addressing and Reporting System, which was originally used to log crew working hours, has since then significantly expanded to include
- ATC (Air Traffic Control) Clearance.
- Information Services (weather)
- Flight Plans
- Positional Reports
- Diagnostic Feeds
- Free-text Messages
- ...
It takes many shapes, is not mandatory but widely used both by public and private actors.
Both of these data communication systems can be relatively easily listened to and decoded from the ground with simple antennas and cheap software-defined radios.
In this article, we will often distinguish between public aircraft, by which I mean commercial passenger airlines, cargo airlines, civilian flights, and non-public aircraft, by which I mean private/business jets, state/military aircraft, diplomatic and special-mission aircraft.
Literature
The research presented here is mainly based on the 5 papers below which will serve as our roadmap:
1 - Undermining Privacy in the Aircraft Communications Addressing and Reporting System (ACARS)
This paper from 2018 discusses the significant privacy leakage that ACARS poses, in particular to private and government stakeholders. A warmly recommended read, whose findings I was able to reproduce on a smaller scale and still hold true in 2026.
2 - Economy Class Crypto: Exploring Weak Cipher Usage in Avionic Communications via ACARS
While the vast majority of ACARS communication is in plain text, some of it (around 1-2%) uses encryption. This encryption however makes use of a mono-alphabetic substitution cipher and thus, is easy to break. The paper sheds light on the phenomenon in 2017, and I could independently confirm that it is still possible to decrypt these messages using the same method at the time of writing.
3 - The Real First Class? Inferring Confidential Corporate Mergers and Government Relations from Air Traffic Communication
This paper from 2018 discusses the potential implications of the privacy leakages discussed above and argues that it is possible to predict mergers and government relations from air traffic communication.
4 - Evading the Public Eye: On Astroturfing in Open Aviation Data
More recently, this paper from 2022 examines how owners and operators of private, corporate, and government aircraft try to evade public tracking, not by fixing the underlying privacy problem, but by requesting removal from tracking platforms or by maliciously editing crowdsourced aircraft databases. The authors argue that such tactics are both real and fairly widespread, yet ultimately mostly useless in the face of decentralized open ADS-B tracking. They also highlight that these efforts can aim to hide information relevant to public scrutiny, including the climate impact of private jet use.
5. Experimental Analysis of Attacks on Next Generation Air Traffic Communication
Finally, this paper explores the feasibility of attacks against ADS-B that go beyond privacy leakage. Message injection, jamming, trajectory manipulation attacks can arguably be carried out with inexpensive hardware. Naturally, I have not attempted to demonstrate nor reproduce any of the paper's arguments, yet it's good to keep in mind that an attacker is not necessarily constrained to the listener role.
Furthermore, On the Security of Satellite-Based Air Traffic Control (ADS-C) and On the Implications of Spoofing and Jamming Aviation Datalink Applications. discuss the potential of active attacks beyond ADS-B.
Setup
To capture and decode ADS-B and ACARS communications over all existing channels, we will need:
- 1-4 RTL-SDRs (depending on how many channels one wants to monitor simultaneously). I used the official v3 RTL-SDRs from rtl-sdr.com. They are available for about $40.
- (Optional) in case of multiple RTL-SDRs, since they need to be powered, a powered USB-Hub can come in handy.
- An antenna that can listen to 1090 MHz for ADS-B
- (Optional) an RF band-pass filter might help reduce unwanted RF energy in urban areas or near airports
- A generic antenna that can listen to 130-140 MHz for ACARS
- A SATCOM patch antenna that can listen to around 1500-1600 MHz for Satellite ACARS
- Coaxial cables to connect the radio side (they are usually delivered together with the antenna)
- Some kind of computer (a Raspberry Pi, your desktop, the slow laptop your friend doesn't use anymore, ...)
If a choice has to be made, as will be explained later down the road, the most interesting channel to investigate is by far the satellite one. One RTL-SDR, one L-Band patch antenna, both going for $30-40, and we are good to go :)
If the budget is tight, the SDR alone can suffice, as antennas can be built in a DIY fashion.
ADS-B
Community
ADS-B tracking is a widely shared passion and numerous community projects exist around it:
- https://globe.adsbexchange.com/
- https://www.flightaware.com/adsb/
- https://www.flightradar24.com/
- https://map.opensky-network.org/
- ...
They provide very pretty live maps of the aircraft flying overhead!

Some of them allow aircraft operators to be anonymized or hidden to varying degrees.
Since evidence shows these data feeds, while reliable for public aircraft, are sometimes blocked and/or poisoned when it comes to private ones, we will try to build our own.
Technicalities
ADS-B data transfer is explained in detail in this book: https://mode-s.org/1090mhz/book-the_1090mhz_riddle-junzi_sun.pdf, but here is the gist of it:
- It operates at 1090 MHz (which means the wave cycles 1090 million times a second. The wave has done a full period in about 0.917 nanoseconds. Crazy!)
- Data is encoded using PPM, Pulse Position Modulation, which in simplified terms works as follows:
Bit time = 1 microsecond
1 bit: |####....| pulse early
0 bit: |....####| pulse lateOne bit is encoded every microsecond. If we get a 0.5 microsecond burst of 1090 MHz radio energy early in the microsecond, we have a 1. If we get a 0.5 microsecond burst of 1090 MHz radio energy late in the microsecond, we have a 0.
The practical implications for us are that it is a line-of-sight radio. The antenna will likely not be able to get clear data packets through walls, hills and too long a distance. Best is to place it high up and with a clear view of the sky whenever possible!
My setup.
On the hardware side, my collection pipeline looked like this:
1090 MHz antenna --> Coax cable --> RF Band-Pass --> RTL-SDR --> Powered USB-Hub --> Raspberry Pi

It is also possible to build the antenna oneself as for example done in this blog: (https://lucsmall.com/2017/02/06/making-antennas-for-1090mhz-ads-b-aircraft-tracking/)

On the software side, to decode ADS-B packets, I used the free and open source project readsb (https://github.com/wiedehopf/readsb). Installing it with apt is not suitable in our case; one has to build it with RTL-SDR support as specified in the documentation. Then it pretty much worked out of the box. A simple systemd logger to take a snapshot every minute, save the results as jsonl, and we were good to go!
Results
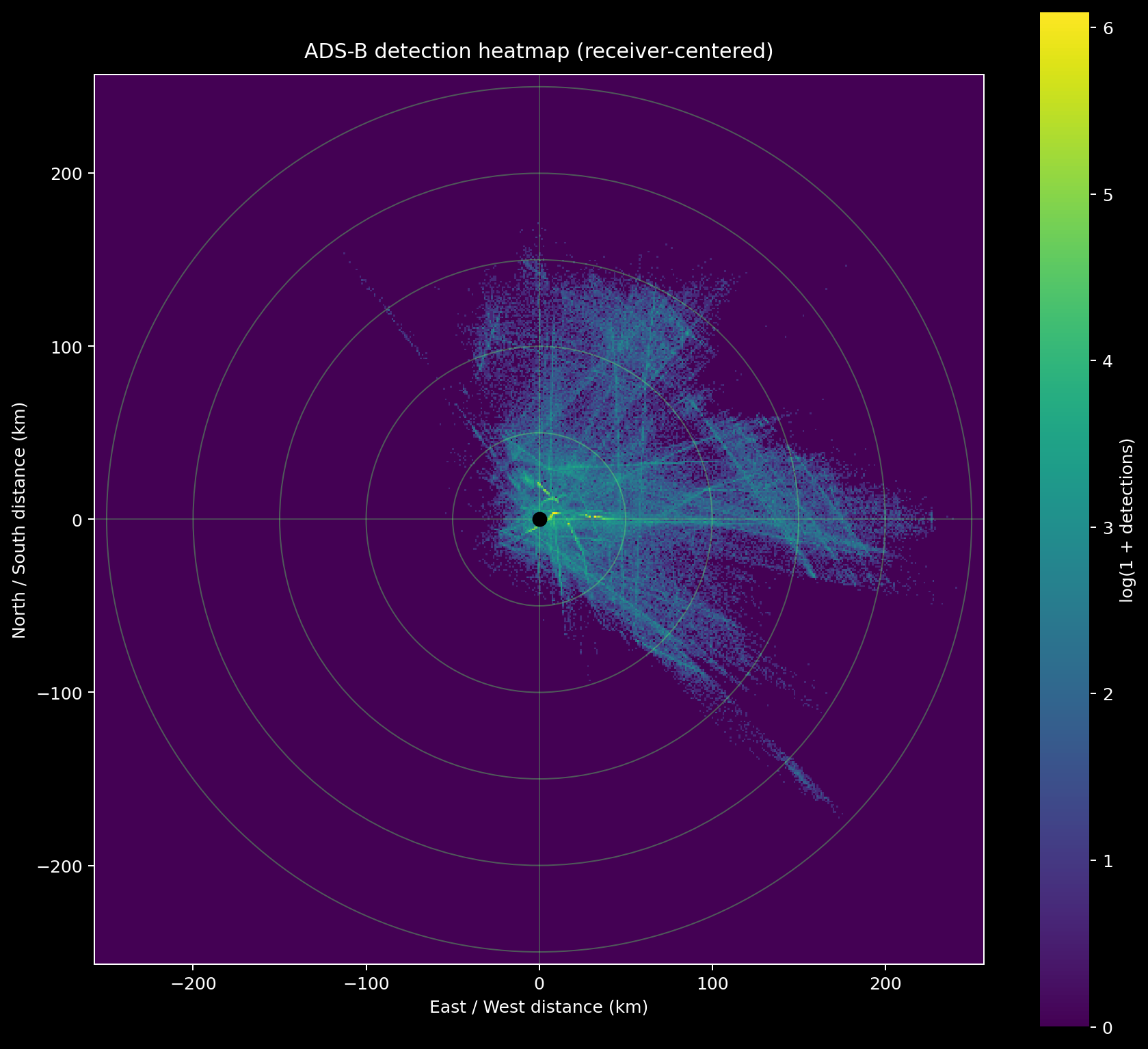
In about 9 days of observation, I was able to see 5510 unique aircraft at a maximum distance of 244.58 km. 83% of messages received included position data.
As we can see on the heatmap, the position of the antenna is very important for successful detection. Mine was at a window, hence why I mostly received data from a single direction:
ADS-B is mandatory for public aircraft and mostly mandatory for business aircraft (public tracking can be reduced and in some contexts it can be turned off). Military aircraft are generally allowed to turn off this automatic position broadcasting.
To identify which planes belong in which category, I used the OpenSky metadata aircraft database (https://opensky-network.org/datasets/metadata/aircraftDatabase.csv) and manually checked entries that I could not match.
From the 5510 planes I could detect, 4822 were public, 466 were private and 46 were government (with 176 aircraft I was not able to confidently identify). 96% of public aircraft came with positional data, 68% of private aircraft and 61% of state/military aircraft. (Whereas 69% of unidentified aircraft came with positional data).
ACARS (VDL)
The goal of my experiment at this stage was to figure out whether there are planes which both turn off ADS-B positional broadcasting for privacy reasons and yet have ACARS messages leaking information about them.
Community
ACARS also has a few community projects around it, the most entertaining one I found being ACARS drama (https://acarsdrama.com/) which gathers and filters messages from all around the world to highlight the spiciest ones.
Protocol
ACARS, the Aircraft Communications, Addressing and Reporting System serves many different purposes, from the management of aircraft fleets to air traffic control. Most of the traffic (around 98-99% from my findings) is in cleartext while some of it is encrypted.
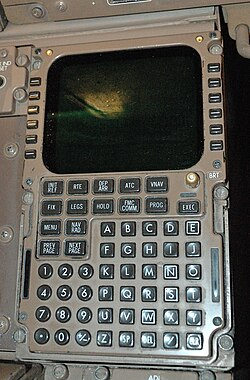
It is also sometimes used to carry out personal messages from cockpits, for example written on flight management systems.
The "Undermining Privacy in the Aircraft Communications Addressing and Reporting System" paper maps the protocol as below:
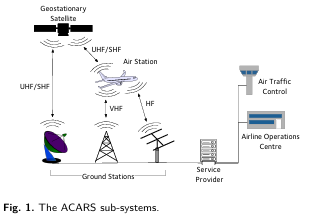
From our position as a passive ground listener, we can realistically hope to catch
- Messages from planes to ground stations, which is the topic of this chapter
- Messages from satellite to aircraft, which is the topic of the next chapter
This protocol is a little more involved than ADS-B. ACARS is not confined to a single frequency but rather represents a family of radio links and can be conveyed through
- VHF, Very high frequency (typically over populated land)
- SATCOM, Satellite communication (typically over oceanic and remote areas)
- HF, high frequency (the least used method)
Technicalities
ACARS messages over VHF can be transmitted either as PoA (Plain old ACARS) or as the newer VDL 2 (Very High Frequency Data Link 2).
In Europe, PoA can be received, for example, at 131.525 MHz, 131.725 MHz, and 131.850 MHz while VDL Mode 2 operates on slightly higher frequencies, as for example 136.725 MHz, 136.775 MHz, 136.875 MHz, and 136.975 MHz.
PoA uses amplitude modulation (AM) to convey data and achieves a speed of around 2400 bits per second.
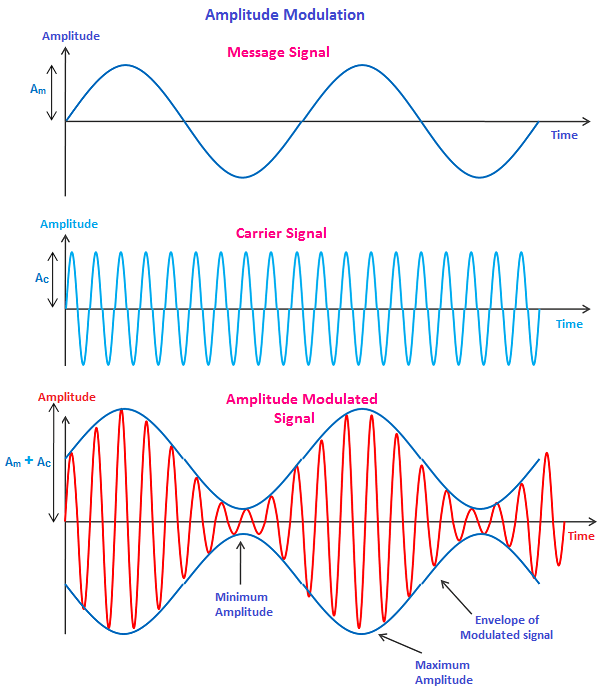
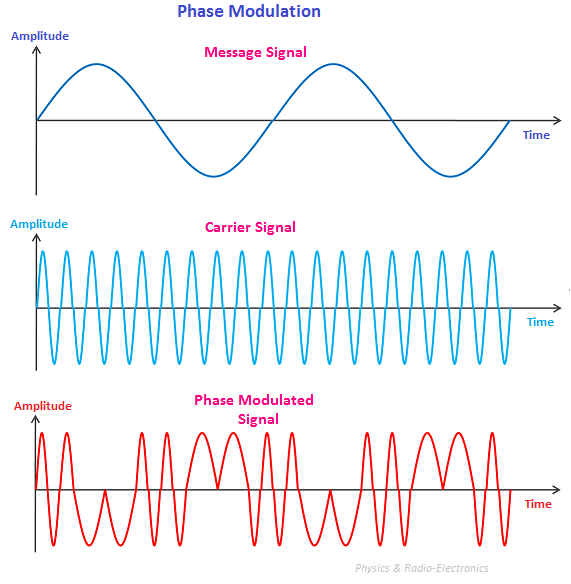
VDL2 encodes data by changing the phase (where the wave is in its cycle) of the radio wave. There are 8 states, defined in advance, and the difference between the current state and the previous state encodes information. This technique brings forth much faster data transmission of around 31,500 bits per second. Therefore, in urban areas especially, it is slowly but surely becoming the main channel of plane-to-ground ACARS messages.
My setup
On the hardware side, my collection setup looked like this:
Simple dipole antenna --> Coax cable --> RTL-SDR --> Powered USB hub --> Raspberry Pi
A dipole antenna works best when its total length matches about half the size of the radio wave it's supposed to catch. A rule of thumb that might sound somewhat magical at first is to divide 143 by the frequency in MHz. Here, since VHF transmits around 131-137 MHz, 143/134 gives us about 1.07 m, 53 cm for each arm. Being a few centimeters off is not dramatic. (https://w0zrt.com/tech-corner/dipole-antenna-calculations/).
We orient it vertically (as the incoming signal is vertically polarized), try our very best not to have too much metal around it, place it high up with a clear line of sight and we are good to go.
It might for example look like this:

On the software side I used acarsdec (https://github.com/f00b4r0/acarsdec/) and dumpvdl2 (https://github.com/szpajder/dumpvdl2).
Before doing anything else, if you are running multiple RTL-SDRs plugged into the same device, I very strongly suggest renaming them. It can otherwise create silly and time-consuming misunderstandings.
The command: rtl_eeprom -d [RTL_Number] -s [Name]
This time, it was less plug-and-play than for ADS-B. Since there are many channels, first, I had to figure out which were the ones active in my area, then which ones were the best. After a quick pass through SDR# (Windows), or GQRX (Linux), I could see that the most active channels in my area are 131.500 MHz, 135.500 MHz, 136.500 MHz and 136.975 MHz. Contrary to ADS-B which transmits continuously, ACARS is bursty, with messages coming in between periods of silence. Depending on your location and the time of the day, some patience might be needed.
The RTL-SDR can monitor multiple frequencies in parallel, but only if they are very close. All PoA frequencies can be captured at the same time, or all VDL2 frequencies, but not both. Fortunately, in my case, after testing it for 2 hours on each mode and monitoring the results, the choice was straightforward.
========== SUMMARY ==========
Hours per mode: 2.00
POA / acarsdec
total messages : 533
messages per hour : 266.5
unique aircraft regs : 24
top labels : [('SQ', 367), ('_d', 76), ('H1', 33), ('SA', 14), ('Q0', 11), ('5V', 7), ('A9', 5), ('1L', 4), ('25', 4), ('B9', 4)]
VDL2 / dumpvdl2
total decoded blocks : 6724
blocks per hour : 3362.0
unique aircraft addrs : 343
top protocol words : [('AVLC', 7033), ('X.25', 5816), ('CLNP', 2653), ('COTP', 2645), ('ACARS', 1217), ('CPDLC', 452), ('ADS-C', 12)]VDL mode 2 it is!
You might notice we are not only receiving ACARS messages, but packets using a wide range of protocols. Familiar-sounding is ADS-C, Automatic Dependent Surveillance Contract. Similar to ADS-B, but used in remote and oceanic areas, we will be capturing and investigating many more of those when pointing our antenna at a satellite!
A systemd logger later, we are now able to continuously monitor and store all incoming messages on 136.675 MHz, 136.725 MHz, 136.775 MHz, 136.825 MHz, 136.850 MHz, 136.875 MHz, 136.900 MHz and 136.975 MHz.
Results
Over the course of 7 days, I was able to receive 528'501 messages in total, 84'127 of which were ACARS messages. Numerous aircraft that were not present in the ADS-B collection could be additionally detected, including 91 identified private/business and 1 state/military aircraft.
Most importantly, while ADS-B only gives an aircraft's position while in detection range, ACARS transmitted weather reports at place of departure and destination, full flight plans and sometimes even passenger lists.
SATCOM
Last but not least, the most delicate, yet the most rewarding data collection method, SATCOM.
Here, instead of capturing data packets from an aircraft intended for ground stations, we capture data packets from a satellite to an aircraft.
Technicalities
Communication happens on L-Band frequencies, around 1540-1550 MHz.
On lower-speed channels, the data is commonly sent using phase modulation between two states to represent bits. On the faster channels, four phase states are used instead.
Hardware
For the hardware side, I used:
L-Band patch Antenna --> Coax --> RTL-SDR --> Powered USB-Hub --> Raspberry Pi
My antenna looked like this:

For it to work, the "face" of the patch antenna has to point towards the satellite, ideally unobstructed. There are currently 4 Inmarsat satellites broadcasting ACARS messages, two of which can be seen from western Europe:
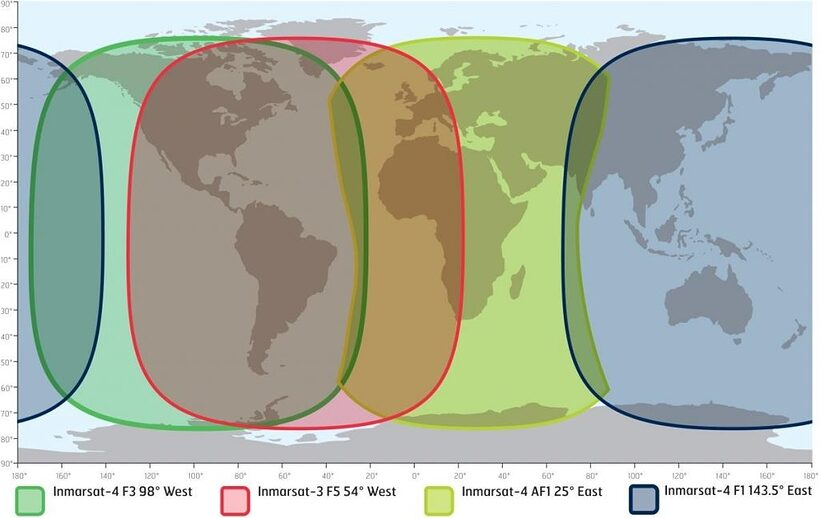
In our case, 25°E seems to be the obvious choice.
These satellites are all geostationary, meaning they rotate at the same speed as the earth, staying above the equator at an almost fixed point in the sky, which makes pointing an antenna at them very feasible.
Orienting the antenna
There are numerous free websites that will give the correct orientation in exchange for your exact location, for example https://www.dishpointer.com/.
If however we insist on doing the maths ourselves, here is how it could work:
The Satellite orbital longitude is known, it's 25.0 degrees East.
Let us take for example an antenna in Paris (48.8566° N, 2.3522° E).
- Calculate the longitude difference:
Δλ = 25.0° - 2.3522° = 22.6478° - Calculate the central angle to the satellite's ground point:
cos(ψ) = cos(48.8566°) × cos(22.6478°) ≈ 0.6579 × 0.9228 ≈ 0.6072ψ = arccos(0.6072) ≈ 52.61°
- Calculate the elevation:
elevation = arctan( (cos(ψ) - R/Rs) / sqrt(1 - cos²(ψ)) ), where R = 6378 km, the earth radius and Rs = 42164 km, the geostationary orbit radius from Earth center.- In our case, elevation ≈ 29.85°
- Calculate the azimuth:
azimuth = atan2( sin(Δλ), -sin(φ) × cos(Δλ) ). In our case, this gives 151° from north clockwise, so south-east.
We get:
- Azimuth: 151° from true north
- Elevation: 29.9°
Additionally, it is often useful to convert the azimuth from true north to magnetic north, which is what a standard compass will point at. For that, we subtract the local magnetic declination from the true azimuth, using east declination as positive and west declination as negative.
The local magnetic declination of any given location can be for example read here: https://www.magnetic-declination.com/. So if Paris has a local declination of about 2.89° East, the magnetic azimuth is approximately 151° - 2.89° ≈ 148°, which is the direction one should follow with a compass.
Final adjustments
After downloading a compass app, discovering there are over 237 legitimate vendors interested in my data while I am searching the north, removing it and installing another, I was able to orient it in roughly the right direction.
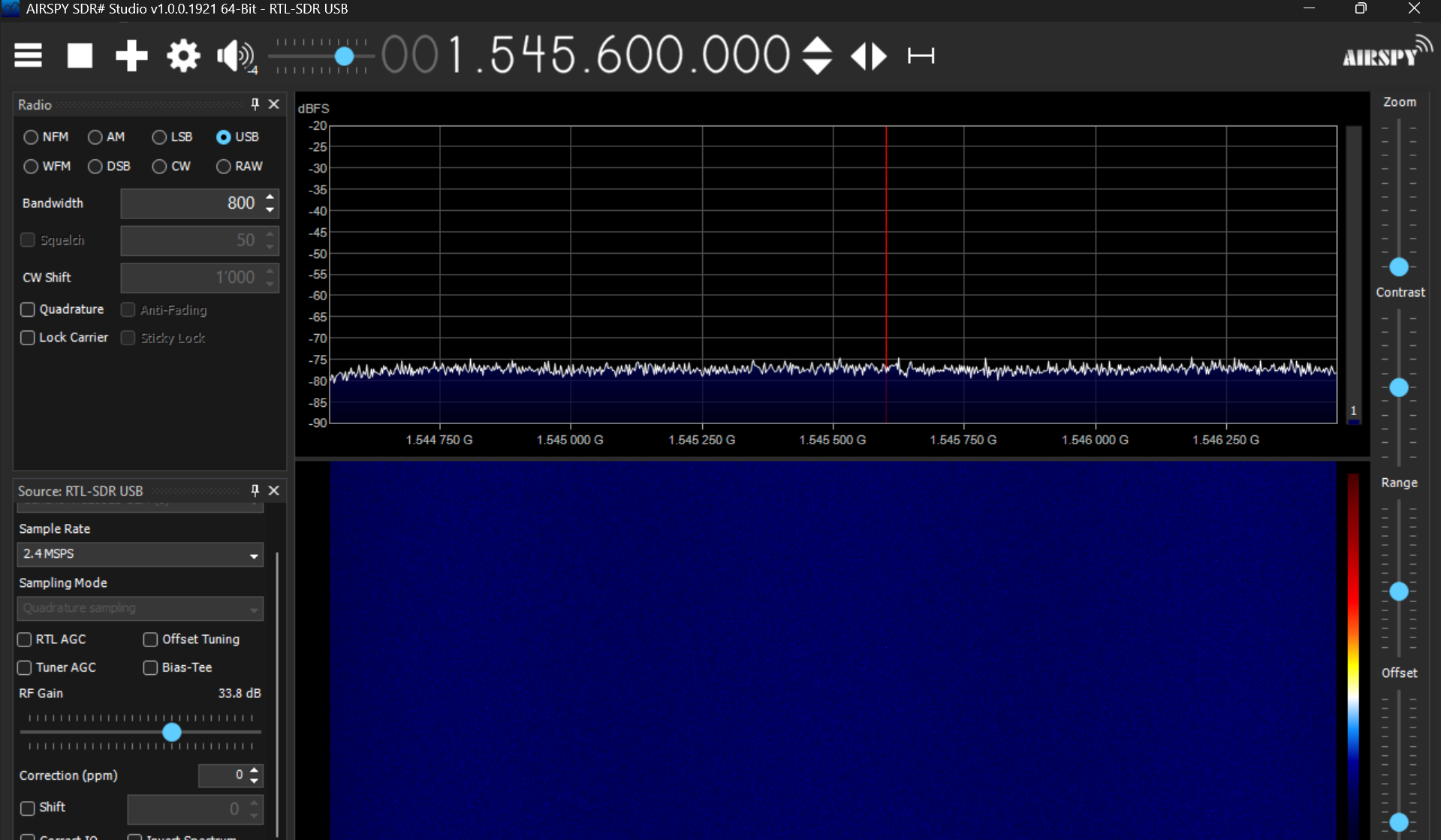
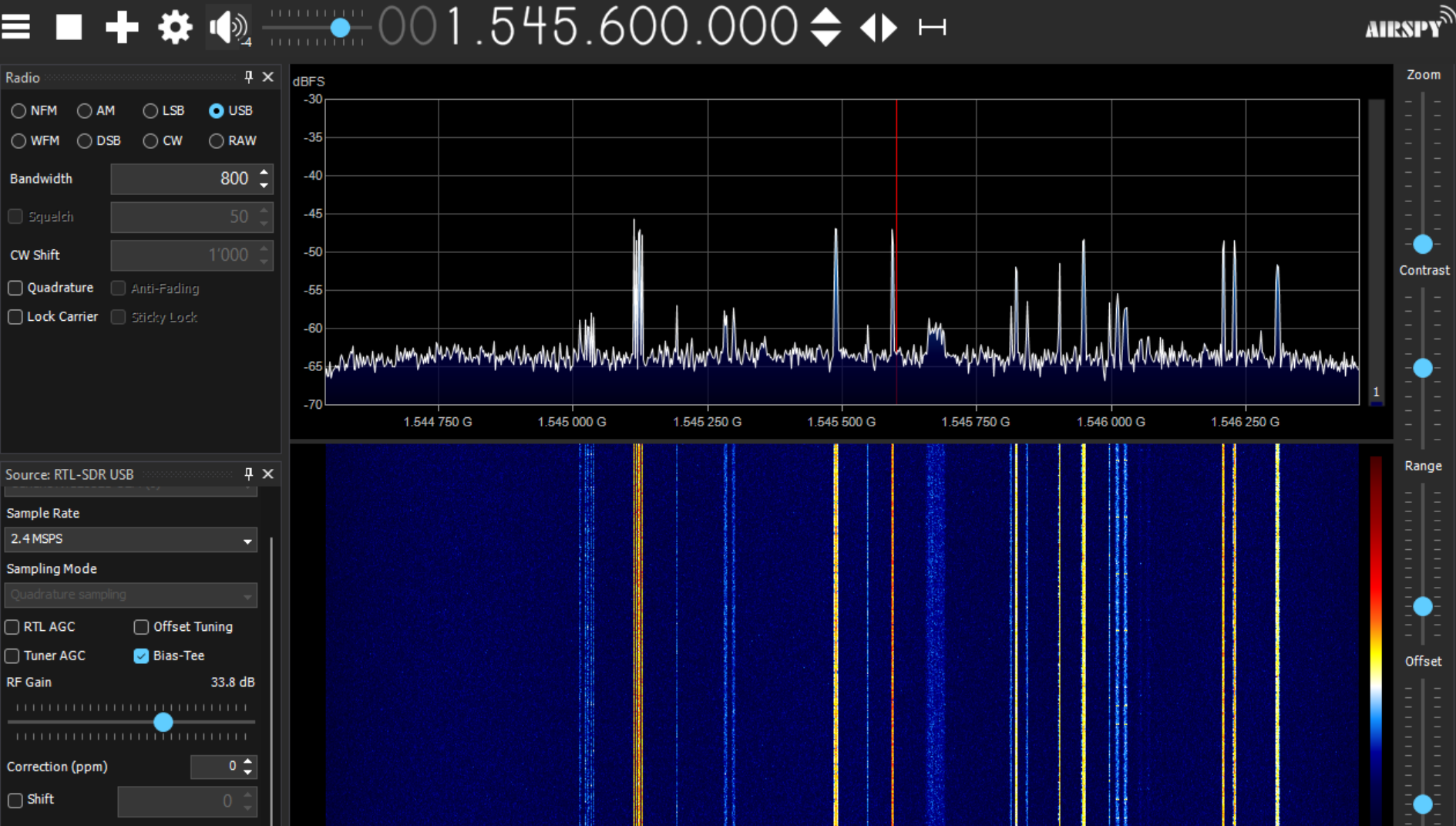
To figure out the optimal positioning, best is to plug in the RTL-SDR and, with SDR# (or GQRX on Linux) open it and look at the live feedback while adjusting the placement.
Software
For the software part it's still fortunately all free and open source :)
If, like me, you end up attempting a headless Linux install to be able to listen on all channels simultaneously, here was my experience:
- Trying to build JAERO (https://github.com/jontio/JAERO) myself has resulted in a failure for reasons I could not debug. Easiest was to use a ready-made Docker image from sdr-enthusiasts: https://github.com/sdr-enthusiasts/docker-jaero. It still required fighting the graphical interface though.
- The headless solution from airframesio didn't work for me but might when the project gets more mature: https://github.com/airframesio/aero-cli
- The generic SatDump tool together with thebaldgeek's wonderful blog (https://thebaldgeek.github.io/) and a lot of tweaking made it work in the end: https://github.com/SatDump/SatDump
However, if exhaustiveness is not a concern, going through Windows and a graphical interface works without any hair-pulling. The best video I found with blindly trustable instructions was this one from Frugal Radio: https://youtu.be/J3Nc9GPOHz0.
He suggests using
- SDR#, to have a visual feedback on what your antenna is receiving and selecting frequency bands
- JAERO to turn radio signal into decoded data
- VB cable to create a virtual cable between the two
It takes trial and error to figure out the right channels and select the right windows to listen on. It is good to keep in mind that
- Not every high-energy channel is dedicated to ACARS. If no data can be decoded despite a clear spike, it might simply not be the right place.
- The lower frequency channels transmit around 600-1200bps while the higher ones transmit around 10500bps.
A list of channels with suggested settings can be found here: https://github.com/jeroenbeijer/SDRReceiver/blob/master/sample_ini/sdr_25E.ini, but frequencies and valid data channels for ACARS seem to change from time to time.
When it works, we can see this:
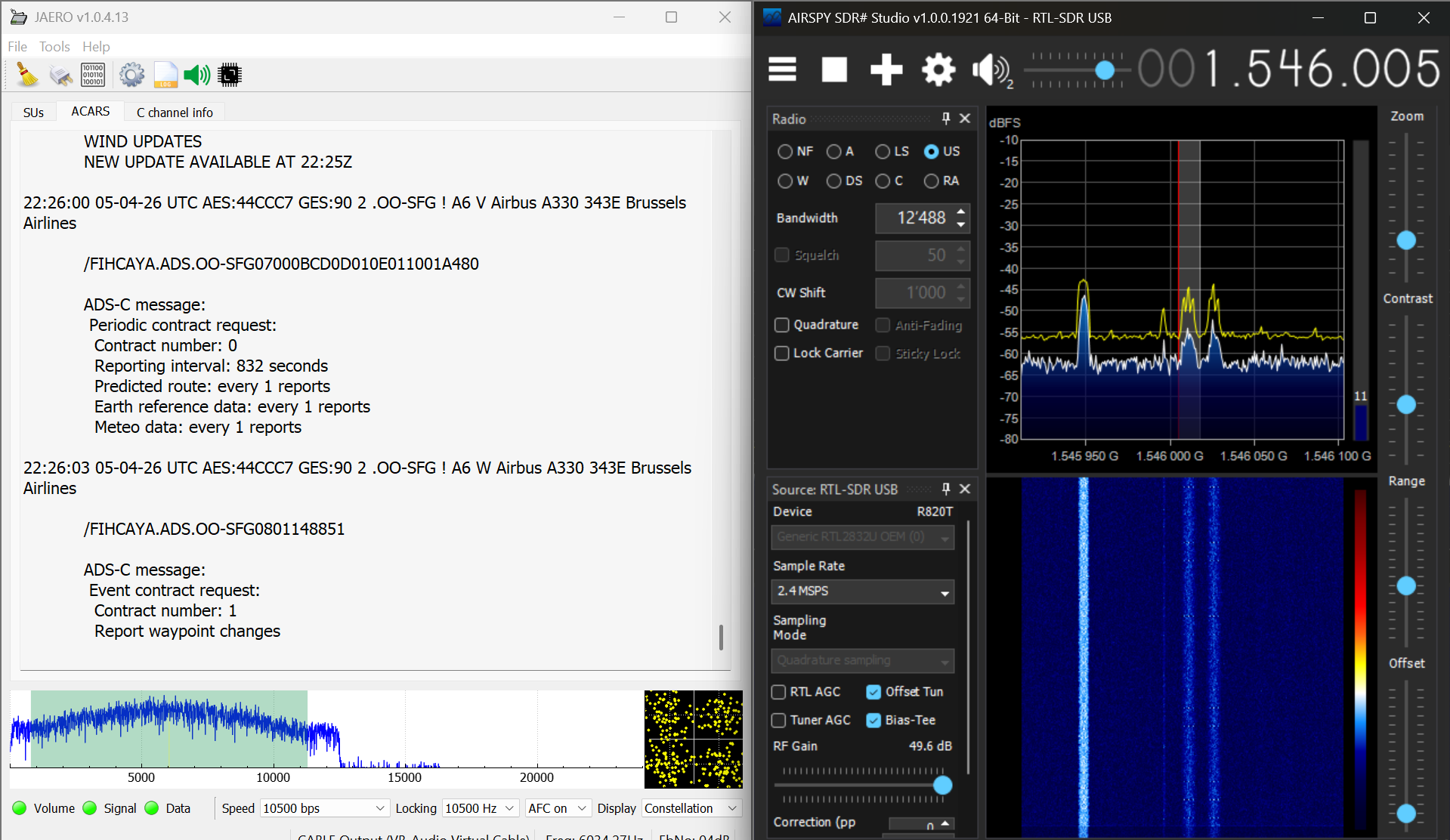
Messages appear at rather high-speed on the left and can be configured to be logged for later analysis.
Results
This method unsurprisingly yields results at a much higher scale than ADS-B and "ground ACARS" since we are no longer constrained by line-of-sight. I received about 1000 unique aircraft detections per high-speed data channel per 3 h of monitoring, combining ACARS and ADS-C. Over a few days, more privacy-sensitive data was collected than I knew what to do with.
Harmless fun
ACARS messages are surprisingly often about birds, medical emergencies or sports results. Sometimes, however, they can be more amusing, eerie or funny. Here is a personal shortlist, stripped of the identifying information:
Text messages
Sometimes, we get messages about the infamous bermuda triangle and smelling planes:
bonsoir, nous sommes equipqage ayant deroute aux bermudes hier, nous voyons sur Flightradar que VC est en vol, est-ce que les collegues ont trouve quelque chose sur l'origine de l'odeur CDB [Redacted Name]
Which translates to
Good evening, we’re the crew who diverted to Bermuda yesterday. We can see on Flightradar that VC is in the air. Have our colleagues found anything regarding the source of the smell CDB [Redacted Name]
Sometimes, we get pilots crashing out over Starlink:
KINDLY DISREGARD THE STARLINK TRIAL DOCUMENT HANDED OVER TO YOU.
Maintenance releases
Apparently, broken furniture is also fixed with tape up there.
DEFECT: TRIM, ASSY FOOTWELL CTR AT SEAT 2L DAMAGED.
ACTION: 11FEB DEF - CONFIRMED PART DAMAGED. ITEM NIS AT GRU.
APPLIED SECURED TAPE ASNECESSARY AND ITEM DOES NOT POSE
ANY HAZARD FOR PASSENGERS AND
ACTION: 11FEB DEF - NEF APPLIED
Advertisement
Ads, they really are everywhere.
Merci d'avoir vole avec FlytOptim.
Depuis le debut du contrat, les equipages de CORSAIR ont economise 102.3 tonnes de carburant.
Votre vol est en cours d'analyse.
Ce message est nouveau.
S'il peut etre ameliore ou si vous avez des idees pour le rendre plus utile en
fin de vol, partagez les ici:
https://myfl.yt/xojo
ISSUED BY THALES
Which translates to
Thank you for flying with FlytOptim.
Since the start of the contract, CORSAIR crews have saved 102.3 tonnes of fuel.
Your flight is currently being analysed.
This message is new.
If it could be improved or if you have any ideas on how to make it more useful at
the end of the flight, please share them here:
https://myfl.yt/xojo
ISSUED BY THALES
Personal information
On one side, there are the weather reports that indirectly leak planes' positions. On the other, it is common to capture detailed personal information about specific passengers. Examples below:
BONSOIR,
LES DEUX BAGAGES DE [REDACTED] SEAT 14H EST DIRECTEMENT ENREGISTRES SUR DLA. PAS BESOIN DE REENREGISTER.
MERCI
BON VOL A VOUS
Translating to
GOOD EVENING,
THE TWO PIECES OF LUGGAGE BELONGING TO [REDACTED] IN SEAT 14H HAVE ALREADY BEEN CHECKED IN ON DLA. THERE IS NO NEED TO CHECK THEM IN AGAIN.
THANK YOU
HAVE A PLEASANT FLIGHT
Or
BONJOUR,
VOUS TROUVEREZ CI-DESSOUS LA LISTE DES CLIENTS SUR VOTRE VOL [REDACTED]
POUR LESQUELS UN ACCUEIL EST PREVU
MERCI DE LES PREVENIR ET DE NOUS LES PRESENTER A L'ARRIVEE
NOM DU CLIENT SIEGE AGENT
[REDACTED LINES]
CORDIALEMENT,SERVICE SCC/KX*
Which translates to
HELLO,
PLEASE FIND BELOW THE LIST OF PASSENGERS ON YOUR FLIGHT [REDACTED]
FOR WHOM A WELCOME IS PLANNED
PLEASE NOTIFY THEM AND INTRODUCE THEM TO US ON ARRIVAL
CUSTOMER NAME SEAT AGENT
[REDACTED LINES]
YOURS FAITHFULLY, SCC/KX DEPARTMENT*
Non-public aircraft
ADS-B
ADS-B leakage was significant already.
On the business side of the sky, I was able to identify personal aircraft belonging to famous personalities such as Acun Ilıcalı's (a famous Turkish TV personality), the Poonawalla family jet (An Indian billionaire who owns the largest vaccine manufacturer in the world) and Michael Bidwill's (president of the Arizona Cardinals of the National (Amercian) Football League (NFL)).
On the military side, the simple setup, in 9 days, was able to detect movements and positions of:
- The US Navy
- The US Air Force
- The Italian Navy
- The Spanish Air Force
- The Force Aerienne Française
- The German Air Force
- The Swedish Air Force
- The Slovenian Territorial Defense Force
- The Swiss Air Force
On the state side, identified with certainty were the movements of:
- A Diplomatic plane from the Swiss Government
- A Diplomatic plane from the Kuwait government
ACARS
ACARS serves as an additional channel to often learn much more about aircraft that already emit ADS-B such as flight plans and sometimes even passenger names. However, from time to time, it is also possible to detect with ACARS aircraft that do not appear on our ADS-B radar.
From the military side of things, with ADS-B fully turned off, I was able to detect movements and infer the position of an aircraft of the Polish Air Force which let out 51 messages in about 9 minutes.
Business-wise, 91 new aircraft were identified that way. In 70 of them, their current or future position could be inferred, sometimes much more.
ACARS (Satellite)
The privacy leakage through this channel is significantly higher yet. In the first 3 hours of logging already, I could identify the positions of aircraft in state-transport / special mission belonging to
- The Government of Azerbaijan
- The Saudi Ministry of Finance
- The Saudi Armed Forces Medical Services
- The Royal Saudi Air Force
- The Government of the Netherlands
- The Royal Moroccan Air Force
- The United States Air Force
- The Royal Air Force
- The French Air Force
- The Kyrgyzstan Government
- ...
"Encrypted" messages
A small portion (around 1-2%) of the ACARS messages received turned out to be encrypted. A not too privacy breaching example of such message would be this one:
22:29:55 05-04-26 UTC AES:A114B1 GES:90 2 .N169SD ! 42 E Gulfstream Aerospace G550 My Jet Ops
TWX0202I,Q---AI;;sE$eX1s$/`
;;sE
sXe|1_$sXe|1$;;sE$,Q-3Q,<$,-,,-oe$q|l;o$-]&--$i3,,A$r;EkO
$e|*_$e|*$;;sE$,Q3],,<$,Q3A&,9-m$l1:,-oe$A,,,$rEq
$:XqsO$,9,9&,9,A$00,3moe
$:XqsO$,939&,93A$-0,,9oe
r;e|s_$;;sE$|,3mA&-9$,-s|1,m,,7-)s|p,m,,
$v|rtkrO$|rt$e|oX$;**$vkskeXt$e;$*v/$14r/|p$;rvp$_
$1/p$,A1&-9v_$*1;s$,m,,$e;$39,,$4eq
$1/p$,Av&-91_$*1;s$39,,$e;$,m,,$4eq
$v|Ee$N4Eh:|qo$-,$skr$N1k;1$1/p$E/keqh;lX1
;;sE$|,303&-9$--*X:,Q-37-0s|p-0Q)
$71X*$|k1|q$|kN$,0&-QI$4EX$;*$N4:vkEhXt$Ee|1E$1/p$,Av&-91$|rt$1/p
$,A1&-9v$eXsN;1|1kvp$E4ENXrtXtT$$|vv$|11klkrO$e1|**kq$q|r$X`NXqe
$1|t|1$lXqe;1E$e;$ehX$|NN1;N1k|eX$k|N
$*;1$*vkOhe$Nv|rrkrO$N41N;EXEI$|vv$|11klkrO$e1|**kq$e;$;;sE$Eh|vv
$*kvX$*vkOhe$Nv|r$1;4eX$e;$sqe$tl;1T
;;sE$|,339&-9$30*X:,],,73-s|p3],,
$q1|rX$/keh$XvXl|ek;r$;*$Q9$*e$/hkqh$kE$s|1oXt$t41krO$ehX$t|p$/kvv
$:X$;NX1|ekrO$/keh$*v/$q;;1tE_
$-009m0T9)9,r$,QA3]Q0TQ0,]X
$-009m,T)0m]r$,QA3]Q0T)9,AX
$-009m-T)-)]r$,QA3]mAT-)3,X
$-009m0T30))r$,QA3]Q9T3)9-X
$*1;s$E*q$e;$Q9*e$|sEv
$*v$&$*v,,3
Nk1XN_$r;$Nk1XNE$*;4rt$*;1$;;sETo approach such messages, the paper mentioned above, Economy Class Crypto: Exploring Weak Cipher Usage in Avionic Communications via ACARS is of great help. Indeed, it argues it is very likely that our message was encrypted using a monoalphabetic substitution cipher, meaning:
- Every plaintext character gets replaced by another character
- The same plaintext character always becomes the same ciphertext character
These ciphers are known to be weak, notably since language has patterns. English for example repeats common words, and letter combinations. Aviation messages repeat even more with, often, pre-defined, predictable formats.
Messages are for instance often introduced with:
- An airport code
- METAR (Weather report)
- TAF (Weather forecast)
- NOTAM (Notice to air missions)
- PIREP (Pilot report)
These repeated structures help us decode messages easily, even by hand!
For example, a few seconds before the encrypted message above, the same aircraft sent a plaintext route-like line containing GISKA ... RADAX ... MCT ... OOMS.
Near the top of our encrypted message appears on a single line: ;;sE - whose pattern matches OOMS exactly! (OOMS is the ICAO (International Civil Aviation Organisation) airport code for Muscat International Airport, which is located in Seeb, Oman).
Then, we see a repeated 6-character word: sXe|1_. Given it is an aviation bulletin, the most likely opening is: METAR: METAR OOMS ...
Right after that, we see ,Q-3Q,<. In a METAR, the next field is usually a timestamp. Keeping track of the substitutions and adding educated guesses, we can slowly but confidently rebuild the whole message.
It is entertaining to do by hand. Yet, the encryption is so weak that your favourite LLM chatbot is probably able to decode it on its own as well.
The fully decoded message here, as a proof of concept:
OOMS
METAR: METAR OOMS 052150Z 02002KT CAVOK 27/22 Q1008 NOSIG
TAF: TAF OOMS 051700Z 0518/0624 VRB02KT 8000 NSC
BECMG 0606/0608 33014KT
BECMG 0616/0618 23006KT
NOTAM: OOMS A0148/26 02MAR0400-29MAY0400
LANDING AND TAKE OFF LIMITED TO FLW RUNWAY ONLY:
RWY 08R/26L: FROM 0400 TO 1600 UTC
RWY 08L/26R: FROM 1600 TO 0400 UTC
LAST PUSHBACK 20 MIN PRIOR RWY SWITCHOVER
OOMS A0131/26 22FEB0521-23MAY2359
-REF AIRAC AIP 03/25, USE OF PUBLISHED STARS RWY 08L/26R AND RWY
08R/26L TEMPORARILY SUSPENDED. ALL ARRIVING TRAFFIC CAN EXPECT
RADAR VECTORS TO THE APPROPRIATE IAP
FOR FLIGHT PLANNING PURPOSES, ALL ARRIVING TRAFFIC TO OOMS SHALL
FILE FLIGHT PLAN ROUTE TO MCT DVOR.
OOMS A0116/26 13FEB0700-12MAY1700
CRANE WITH ELEVATION OF 56 FT WHICH IS MARKED DURING THE DAY WILL
BE OPERATING WITH FLW COORDS:
233643.6960N 0581753.5307E
233640.9347N 0581753.9608E
233642.9297N 0581748.2910E
233643.1399N 0581756.1962E
FROM SFC TO 56FT AMSL
FL / FL001
PIREP: NO PIREPS FOUND FOR OOMSThe substitution we get is good to store. Indeed, as only 9 different keys could be observed, it is likely to save us precious time when decoding future messages.
Substitution table
$ → (space)
& → /
) → 9
* → F
, → 0
- → 2
/ → W
0 → 3
1 → R
3 → 1
4 → U
7 → -
9 → 6
: → B
; → O
< → Z
A → 8
E → S
I → ,
N → P
O → G
Q → 5
T → .
X → E
] → 7
_ → :
` → X
e → T
h → H
i → Q
k → I
l → V
m → 4
o → K
p → Y
q → C
r → N
s → M
t → D
v → L
| → AThe original paper found encrypted status reports, airport information, free text messages and meteorological reporting, all of which constitute significant privacy leakage. They were able to recover 95.2% of the substitutions across the 9 keys, which enables also decoding messages that are shorter and offer less clues / context to work with. It further claims that, with enough time/data, they would be able to recover every single message.
In the data I sampled, the vast majority of encrypted messages (>80%) came from non-public aircraft.
Consequences
We have already shown that, with relatively cheap equipment, it is possible to
- Leak the position of business, state and military aircraft
- Learn personal information about specific passengers on public as well as private aircraft
- Trivially decrypt supposedly encrypted communication
The paper The Real First Class? Inferring Confidential Corporate Mergers and Government Relations from Air Traffic Communication argues that this data can reveal private and confidential actions by businesses and states alike.
The sky so reveals diplomatic relations, short term by leaking meetings between officials and, long-term, by enabling a quiet mapping of government relationships.
Mergers and acquisitions cases are also likely to be leaked that way, as the buyer's corporate aircraft is likely to visit the target before the official announcement, opening the door for market distortion, insider trading, and putting the actors involved under strategic risk.
While malicious interference on open datasets (blocking, poisoning, etc.) has been attempted by concerned actors, it should "eventually remain futile" (Evading the Public Eye: On Astroturfing in Open Aviation Data) due to the decentralized nature of these networks.
Active attacks
The plaintext nature of these communications paves the way for more active attacks than mere privacy leakage through passive listening.
ADS-B
The examples below are directly taken from and demonstrated in the following paper: Experimental Analysis of Attacks on Next Generation Air Traffic Communication.
Ghost Aircraft Injection
Broadcasting believable ADS-B messages about non-existing aircraft could potentially force pilots and controllers into life-threatening confusion in low-visibility settings, deny landing and force aircraft to change course.
Ghost Aircraft Flooding
Based on the same attack as above but this time with many aircraft, which do not necessarily have to be believable. The goal could be to carry out a denial-of-service attack on
the controller’s surveillance system.
Virtual Trajectory Modification
By either deleting and injecting ADS-B messages, or modifying them, it could be possible to modify the trajectory of an existing in-flight aircraft.
False Alarm Attack
ADS-B has in-built mechanisms to indicate that an aircraft is in distress, for example in the case of a hijack. Modifying ADS-B messages could trigger such alarms, making given airplanes unable to land and creating confusion. Since the radio of a hijacked plane is per protocol to be considered untrustworthy, restoring the situation may prove tricky.
Ground Station Flooding
History has shown that without the support of collision avoidance systems, collisions are likely to happen, especially around airports during climbing or descending phases. Continuous jamming attacks on a ground sensor or aircraft make such systems fail.
Aircraft Disappearance
By deleting all messages of a target aircraft, an attacker can make it "disappear". If detected, it is likely to force its landing. If not detected, the aircraft is not protected anymore by collision-avoidance technology which could be fatal.
Aircraft Spoofing
The ICAO (International Civil Aviation Organisation) address of an aircraft (a unique 24-bit identifier) can be reprogrammed to masquerade as a friendly aircraft in enemy territory.
ADS-C
The examples below are directly based on the paper On the Security of Satellite-Based Air Traffic Control (ADS-C).
Denial of Service
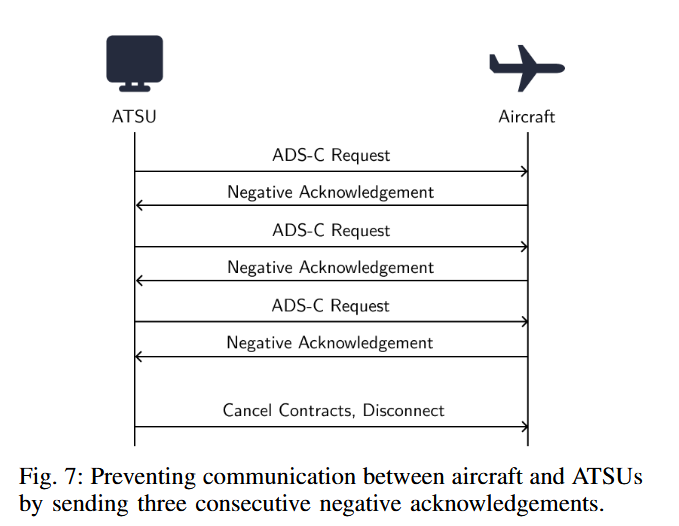
An active downlink attacker has many ways to initiate a denial of service attack. An attacker can for instance achieve it by:
- Sending an aero log-off message
- Sending 3 negative acknowledgments, pretending that valid messages are not acceptable, which will shut down the link
- Interfering with the log-on handshake at setup time, preventing the aircraft from entering the ADS-C service in the first place.
- Cancelling existing contracts, making the aircraft no longer send the expected surveillance reports.
Spoofing
An attacker can inject forged ADS-C reports containing fake latitude, longitude, and altitude values. The idea can be pushed further by altering not only position, but also speed, heading, waypoints, or intended route, making the aircraft appear to be following an entirely different trajectory.
Emergency Reporting Manipulation
Pilots can trigger an ADS-C emergency reporting mode. An attacker can imitate that behavior and force aircraft into emergency-style reporting when no real emergency exists. This creates confusion and additional workload for controllers and can drown attention in false urgency. The opposite attack is also possible. If an aircraft is in emergency mode, an attacker can send a forged message cancelling it, restoring the normal reporting interval and potentially suppressing information that should have remained visible during a real emergency.
The paper classifies several of these attacks, especially link disruption and false surveillance injection, as high-impact under the right conditions. The likely result is not an immediate Hollywood-style catastrophe, but confusion, loss of situational awareness, extra workload for ATC, etc.
ACARS
Methods described for the two protocols above can be similarly applied in the case of ACARS. The paper On the Implications of Spoofing and Jamming Aviation Datalink Applications by Harshad Sathaye, Guevara Noubir and Aanjhan Ranganathan shows that an attacker can spoof ACARS messages and selectively jam legitimate ones from a particular aircraft with a reaction time of 1.48 ms and 98.85% jamming success.
While in this case it targets less automated systems, it is not hard to imagine spoofed messages influencing crew decision in mission-critical contexts, magnifying the threat when combined with attacks on other avionics. It argues that, "till date, these critical systems remain vulnerable and qualify as prime targets".
A future for privacy in aviation?
ADS-B and ACARS were likely designed with a threat model that assumed little to no malicious activity. On top of that, the relatively recent democratization of software-defined radios transformed aviation signals from technically public but difficult to access into something cheaply receivable by almost anyone, setting the scene up for a perfect storm.
Eventually, moving toward data-links with network-level security (authentication, encryption, integrity, replay protection, ...) seems to be the unavoidable solution.
Since 2018, more secure IP-based successors or overlays such as SwiftBroadband-Safety and Iris have appeared. However, legacy ACARS remains the default. At the time of writing, less than 5% of aircraft were equipped with this technology. (https://www.viasat.com/aviation/flight-operations-and-safety/swiftbroadband-safety-sb-s/)
Conclusion
Starting this project, I was full of doubts and had never touched a software-defined radio before. In the end, it turns out that we were able to:
✓ Track airplanes above us with ADS-B
✓ Receive plaintext messages with ACARS
✓ Reproduce, almost 10 years later, the papers' results arguing that both these systems leak significant, exploitable private information about corporate, military and government entities
✓ Receive encrypted messages from a Satellite
✓ Decipher said encrypted messages
Free and open source software is truly amazing! And the security situation.. frankly unsettling ^^'
In the meantime, waiting for aviation to fix its privacy issues, I might join one of the community projects, or dig a little deeper and come back with another adventure!
A pilot who says he has never been frightened in an airplane is, I’m afraid, lying.
~ Louise Thaden
References
- Smith, Matthew & Moser, Daniel & Strohmeier, Martin & Lenders, Vincent & Martinovic, Ivan. (2018). Undermining Privacy in the Aircraft Communications Addressing and Reporting System (ACARS). Proceedings on Privacy Enhancing Technologies. 2018. 105-122. 10.1515/popets-2018-0023.
- Smith, Matthew & Moser, Daniel & Strohmeier, Martin & Lenders, Vincent & Martinovic, Ivan. (2017). Economy Class Crypto: Exploring Weak Cipher Usage in Avionic Communications via ACARS.
- M. Strohmeier, M. Smith, V. Lenders and I. Martinovic, "The Real First Class? Inferring Confidential Corporate Mergers and Government Relations from Air Traffic Communication," 2018 IEEE European Symposium on Security and Privacy (EuroS&P), London, UK, 2018, pp. 107-121, doi: 10.1109/EuroSP.2018.00016. keywords: {Aircraft;Military aircraft;Privacy;Government;Tracking;Stakeholders;air traffic communication;privacy;open source intelligence},
- Strohmeier, M.; Olive, X.; Sun, J. Evading the Public Eye: On Astroturfing in Open Aviation Data. Eng. Proc. 2022, 28, 7. https://doi.org/10.3390/engproc2022028007
- Schäfer, M., Lenders, V., Martinovic, I. (2013). Experimental Analysis of Attacks on Next Generation Air Traffic Communication. In: Jacobson, M., Locasto, M., Mohassel, P., Safavi-Naini, R. (eds) Applied Cryptography and Network Security. ACNS 2013. Lecture Notes in Computer Science, vol 7954. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-38980-1_16
- Lüscher, T., Strohmeier, M., Lenders, V. (2024). On the Security of Satellite-Based Air Traffic Control (ADS-C). In: Proceedings of the 2nd Workshop on the Security of Space and Satellite Systems (SpaceSec 2024), San Diego, California.
- Sathaye, H., Noubir, G., Ranganathan, A. (2022). On the Implications of Spoofing and Jamming Aviation Datalink Applications. In: Annual Computer Security Applications Conference (ACSAC 2022).